Various locations like airports, hotels, coffee shops, and even retail centers provide public charging stations for the convenience of powering up your smartphone or laptop.
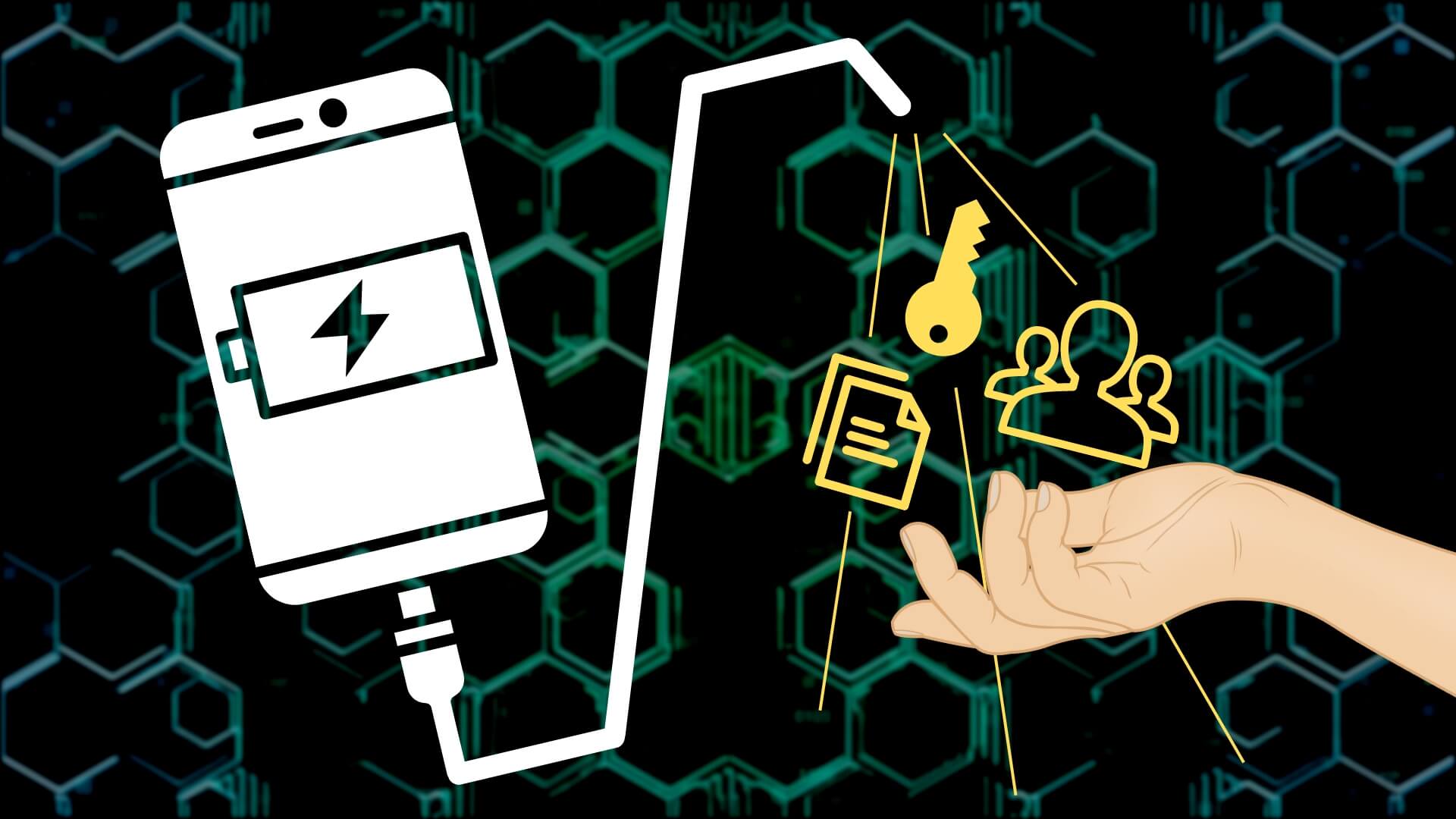
These charging points have recently made headlines after the FBI issued a cautionary tweet advising against their use. It appears that miscreants have discovered how to manipulate USB ports to implant malicious software and surveillance programs on devices while they recharge.
The concept of "juice jacking" had been widely regarded as a hypothetical threat rather than a genuine one. Still, with the availability of smaller, more affordable, and easier-to-operate technology, even less skilled criminals have started capitalizing on this technique.
So, what's the mechanism behind it?
Standard charging cables such as USB-C and lightning serve two functions. They contain pins for both power transmission and data exchange.
When you power up your gadget, only the charging pins are engaged. However, without your knowledge, a tampered charging port or a left-behind cable could leverage the power and data pins.
The moment you connect your device, cybercriminals can utilize these data pins; they can deploy malware onto your device, granting them access to your login details and other sensitive information. This scenario is comparable to connecting your phone to a stranger's computer.
Carrying your own charging equipment and using a power socket is always best to sidestep this threat. If you find yourself in a situation where you need to use a public USB port, consider investing in a USB data blocker. It inhibits data from being exchanged while allowing your device to charge.
Our mission is to eliminate business cyber risks; connect with us if we can help you.